In this article I want to talk about one of my tech adventures from shortly after I went on vacation, which is that of getting OpenVPN up and running and using it to contact the TunnelBear servers. TunnelBear is a paid VPN service that provides both end-to-end VPN encryption and anonymous proxying, using AES-256 encryption for all connections, and collects only a bare minimum of data from customers. It’s also the VPN I am subscribed to. I’m going to talk about my personal experience establishing TunnelBear service through OpenVPN. There are a lot of VPN services out there, but I will focus on TunnelBear since I’d like to be able to get into the nitty-gritty details of my experience rather than having to be vague and general in an effort to be widely applicable.
I swear by paid VPNs as opposed to free VPNs, because free VPNs almost universally collect massive amounts of data on you and use that data to bombard you with ads. And due to the magic of subpoenas and B2B Big Data marketing, that data is instantly available to governments and corporations whenever they want it, so in practice using a free VPN isn’t any safer than using no VPN at all. In fact it may even be less safe. The only difference is which companies are collecting your data. Seriously, free VPNs are a joke, a literal scam. Never ever use one under any circumstances.
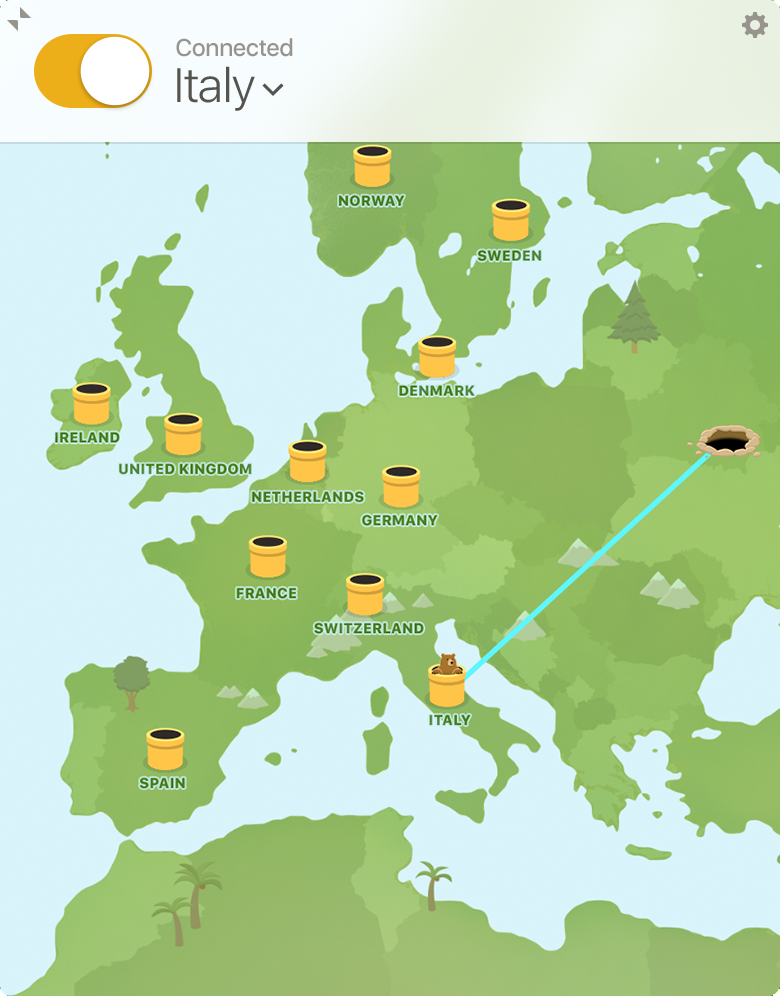
TunnelBear is a paid VPN, and for the most part I like it. I do have to turn it off when posting to certain sites like 4Chan that interpret VPN traffic as spam or abusive content, which is a major pain in the ass, but other than that it serves its function rather well. The actual VPN client software, however, still leaves much to be desired. It’s not very customizable and it tends to stop working at random times, and when it gets disconnected, it takes a really long time to reconnect, if it’s able to reconnect at all.
That’s one reason why I wanted to find an alternative to the stock TunnelBear client. The other reason is just the simple fact that the client won’t run on Linux. One of the projects I’ve been working on lately is creating a system where I can be as anonymous as possible while doing hacky stuff on the Internet through Tails. This involves a philosophy of complete overkill, where a user combines tools like Tor, multiple VPNs, multiple SOCKS proxies, anti-fingerprinting techniques, etc. in combination to minimize the chances of being deanonymized. So far I’ve managed to combine Tor with proxychains so that after a packet leaves the Tor network, it goes through a series of anonymous SOCKS proxies before reaching its destination (I will talk about this part of the project in another post).
My next step is to add end-to-end encryption with a VPN. People who are in the Cypherpunk/Internet privacy community will be familiar with the Tor exit node vulnerability, where data is completely decrypted as it leaves the exit node and can thus be intercepted if the exit node is controlled by a hostile entity. Cypherpunks will be equally familiar with the solution to this vulnerability, which is to use end-to-end encryption via a VPN. Since there is no TunnelBear client for Linux (and the same is true of a number of other VPN services I would wager), I will have to set up the VPN client myself using a generic VPN software like OpenVPN.
OpenVPN is an open source VPN daemon written by James Yonan. It is built heavily on the OpenSSL library, and is largely a modification of the SSL/TLS protocol. The software is capable of implementing either a VPN server or a VPN client. In this case I want to implement a client. OpenVPN is flexible in other ways as well, allowing endpoints to authenticate using either PKI-style certificates or P2P-style pre-shared key authentication. It is customizable through config files using the .ovpn extension, of which there may be dozens or even hundreds. Typically you would have a separate config file for each VPN server you want to connect to.
When looking to port TunnelBear to Linux, I did a quick web search and landed on this page from the TunnelBear company. I wasn’t able to follow the instructions on that page since apt isn’t working in my Tails installation (I’ve had a lot of problems with apt: it works fine in Ubuntu but nowhere else). So I had to improvise. I figured I’d start off installing the OpenVPN software in Windows first since the process would be more straightforward, then graduate to the challenge of installing OpenVPN in Tails without a package manager. I started at the OpenVPN website and downloaded the installer for Windows 7. Once installation is complete, you get an item in your start menu to generate an OpenVPN static key. I clicked on that menu item and got this:

I looked up errno code 5 in my Open Watcom libraries and it looks like it corresponds to ENOMEM. Not sure what that means. I opened up the settings panel for the OpenVPN GUI and found that it has a designated folder for config files and a designated folder for log files.

Okay, good to know. I then looked at this page and got the instructions for starting up OpenVPN from the command line.
openvpn --config myvpn.conf
That was confusing. I wasn’t sure whether the extension was supposed to be .conf or .ovpn. I looked at the settings again. It said ovpn. I started creating my config file, but halfway through realized that I needed the address for the TunnelBear server. I went back to that TunnelBear page, where I knew I would be most likely to find that information. Turns out the page gives a link to a Zip file containing all of the configurations for the different servers, as well as the TunnelBear public key. I downloaded that and changed my config path. Then I started up OpenVPN from the command prompt.

I needed my TunnelBear login credentials. Unfortunately I hadn’t used my username or password since signing up for TunnelBear, so I had to open up my email inbox, go to the confirmation email for my TunnelBear account, and follow the link to login. I looked at the “Change Password” prompt. My username was just my email address and my password was 28 characters. I have only one 28 character password that I use, so I immediately knew what it was. I entered my login information and was successfully logged in.

Buncha console messages and gobbledigook. At this point I’m not sure what’s going on. The program ran for about a minute and then exited without any change in my connectivity status, but when I went to the system tray and right-clicked on the OpenVPN icon, I noticed that it had added all my TunnelBear servers. I went to the first one (Australia) and it brought up this window:

Once I entered my login information, my connectivity status changed, indicating that I was logged into the VPN server. Success!
Now let’s move on to Linux. I knew that I wouldn’t be able to follow the TunnelBear page’s instructions exactly due to my package manager not working in Tails. So I decided to improvise by first downloading OpenVPN in Arch Linux and then manually copying the files into the Tails filesystem. Since pacman is a binary-based package manager using simple tarballs for distribution, no compilation would be necessary, and all I had to do to install the package in Tails was unpack the tarball and copy its contents to the appropriate directories. When in Arch Linux I wanted to download the package without actually installing it. I just wanted the original tarball. So I did as follows:
$ pacman -Sw openvpn
I then copied the two package files that were downloaded (OpenVPN plus a single dependency) from the cache directory to my SD card on /dev/sdd1. Once the package files were safely on permanent storage, I rebooted into tails. There I went to the SD card and started unpacking and copying.
$ unxz *
$ tar -xf openvpn*
$ sudo cp usr/bin/* /usr/bin
$ sudo cp -R usr/lib/* /usr/lib
$ sudo cp usr/include/* /usr/include
$ sudo cp usr/share/man/man8/* /usr/share/man/man8
…Or something like that.
At this point I attempted to start up OpenVPN, but found that what I had done was not enough because there were still dependencies missing. A library file called libpkcs11-helper.so.1 was needed but could not be found. There are probably other library files that I need as well. These are probably files that are dependencies of OpenVPN but were not downloaded by pacman because they were already on the Arch Linux filesystem. I will have to find them.
Anyway, that’s as far as I’ve gotten for now. I abandoned this project during the summer, but I’ve recently started working with Tails again, so I will try picking up where I left off. I’ll be sure to keep my readers updated on my progress.

hey googled into this page. i got tunnelbear working on my raspberry pi 4/Debian openvpn cli using the instructions here https://wiki.archlinux.org/title/TunnelBear
LikeLike
Yeah, I would typically suggest that people use other sources besides this page, since the article I’ve written here is over two years old and is horrendously out-of-date. I don’t know why Google is still ranking this page. Good to see other people have picked up the slack though.
LikeLike